【安全算法之SHA512】SHA512摘要运算的C语言源码实现
- 概述
- 头文件定义
- C语言版本的实现源码
- 测试用例
- github仓库
- 更多参考链接
概述
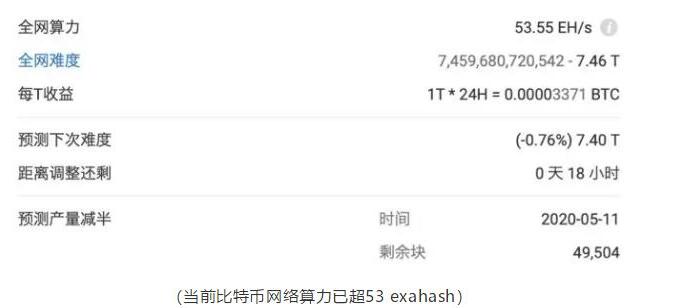
大家都知道摘要算法在安全领域,也是一个特别重要的存在,而SHA512是其中比较常见的一种摘要算法,它的特点就是计算复杂度较低,不等长的数据原文输入,可以得出等长的摘要值,这个值是固定为64字节。正是由于这种特殊性,很多重要的数据完整性校验领域,都可以看到SHAxxx的影子。由于它的摘要值长度比较长,且相对于其他SHA算法,它的计算复杂度会高些,所以使用场景不算特别多。
今天给大家带来SHA512的C源码版本实现,欢迎大家深入学习和讨论。
头文件定义
头文件定义如下,主要定义了SHA512的上下文结构体,以及导出的三个API:
#ifndef __SHA512_H__
#define __SHA512_H__
#include
#define SHA512_DIGEST_LEN 64 // SHA512 outputs a 64 byte digest
typedef struct _sha512_ctx_t {
uint64_t total[2]; /*!< number of bytes processed */
uint64_t state[8]; /*!< intermediate digest state */
uint8_t buffer[128]; /*!< data block being processed */
int32_t is_384; /*!< 0 => SHA-512, else SHA-384 */
} sha512_ctx_t;
void crypto_sha512_init(sha512_ctx_t *ctx);
void crypto_sha512_update(sha512_ctx_t *ctx, const uint8_t *data, uint32_t len);
void crypto_sha512_final(sha512_ctx_t *ctx, uint8_t *digest);
#endif // __SHA512_H__
C语言版本的实现源码
下面是SHA512的C语言版本实现,主要也是围绕导出的3个API:
#include
#include "sha512.h"
#if defined(_MSC_VER) || defined(__WATCOMC__)
#define UL64(x) x##ui64
#else
#define UL64(x) x##ULL
#endif
#define SHA512_VALIDATE_RET(cond) \
do { \
if( !(cond) ) \
{ \
return( -1 ); \
} \
} while( 0 )
#define SHA512_VALIDATE(cond) \
do { \
if( !(cond) ) \
{ \
return; \
} \
} while( 0 )
/*
* 64-bit integer manipulation macros (big endian)
*/
#ifndef GET_UINT64_BE
#define GET_UINT64_BE(n,b,i) \
{ \
(n) = ( (uint64_t) (b)[(i) ] << 56 ) \
| ( (uint64_t) (b)[(i) + 1] << 48 ) \
| ( (uint64_t) (b)[(i) + 2] << 40 ) \
| ( (uint64_t) (b)[(i) + 3] << 32 ) \
| ( (uint64_t) (b)[(i) + 4] << 24 ) \
| ( (uint64_t) (b)[(i) + 5] << 16 ) \
| ( (uint64_t) (b)[(i) + 6] << 8 ) \
| ( (uint64_t) (b)[(i) + 7] ); \
}
#endif /* GET_UINT64_BE */
#ifndef PUT_UINT64_BE
#define PUT_UINT64_BE(n,b,i) \
{ \
(b)[(i) ] = (uint8_t) ( (n) >> 56 ); \
(b)[(i) + 1] = (uint8_t) ( (n) >> 48 ); \
(b)[(i) + 2] = (uint8_t) ( (n) >> 40 ); \
(b)[(i) + 3] = (uint8_t) ( (n) >> 32 ); \
(b)[(i) + 4] = (uint8_t) ( (n) >> 24 ); \
(b)[(i) + 5] = (uint8_t) ( (n) >> 16 ); \
(b)[(i) + 6] = (uint8_t) ( (n) >> 8 ); \
(b)[(i) + 7] = (uint8_t) ( (n) ); \
}
#endif /* PUT_UINT64_BE */
/*
* Round constants
*/
static const uint64_t K[80] =
{
UL64(0x428A2F98D728AE22), UL64(0x7137449123EF65CD),
UL64(0xB5C0FBCFEC4D3B2F), UL64(0xE9B5DBA58189DBBC),
UL64(0x3956C25BF348B538), UL64(0x59F111F1B605D019),
UL64(0x923F82A4AF194F9B), UL64(0xAB1C5ED5DA6D8118),
UL64(0xD807AA98A3030242), UL64(0x12835B0145706FBE),
UL64(0x243185BE4EE4B28C), UL64(0x550C7DC3D5FFB4E2),
UL64(0x72BE5D74F27B896F), UL64(0x80DEB1FE3B1696B1),
UL64(0x9BDC06A725C71235), UL64(0xC19BF174CF692694),
UL64(0xE49B69C19EF14AD2), UL64(0xEFBE4786384F25E3),
UL64(0x0FC19DC68B8CD5B5), UL64(0x240CA1CC77AC9C65),
UL64(0x2DE92C6F592B0275), UL64(0x4A7484AA6EA6E483),
UL64(0x5CB0A9DCBD41FBD4), UL64(0x76F988DA831153B5),
UL64(0x983E5152EE66DFAB), UL64(0xA831C66D2DB43210),
UL64(0xB00327C898FB213F), UL64(0xBF597FC7BEEF0EE4),
UL64(0xC6E00BF33DA88FC2), UL64(0xD5A79147930AA725),
UL64(0x06CA6351E003826F), UL64(0x142929670A0E6E70),
UL64(0x27B70A8546D22FFC), UL64(0x2E1B21385C26C926),
UL64(0x4D2C6DFC5AC42AED), UL64(0x53380D139D95B3DF),
UL64(0x650A73548BAF63DE), UL64(0x766A0ABB3C77B2A8),
UL64(0x81C2C92E47EDAEE6), UL64(0x92722C851482353B),
UL64(0xA2BFE8A14CF10364), UL64(0xA81A664BBC423001),
UL64(0xC24B8B70D0F89791), UL64(0xC76C51A30654BE30),
UL64(0xD192E819D6EF5218), UL64(0xD69906245565A910),
UL64(0xF40E35855771202A), UL64(0x106AA07032BBD1B8),
UL64(0x19A4C116B8D2D0C8), UL64(0x1E376C085141AB53),
UL64(0x2748774CDF8EEB99), UL64(0x34B0BCB5E19B48A8),
UL64(0x391C0CB3C5C95A63), UL64(0x4ED8AA4AE3418ACB),
UL64(0x5B9CCA4F7763E373), UL64(0x682E6FF3D6B2B8A3),
UL64(0x748F82EE5DEFB2FC), UL64(0x78A5636F43172F60),
UL64(0x84C87814A1F0AB72), UL64(0x8CC702081A6439EC),
UL64(0x90BEFFFA23631E28), UL64(0xA4506CEBDE82BDE9),
UL64(0xBEF9A3F7B2C67915), UL64(0xC67178F2E372532B),
UL64(0xCA273ECEEA26619C), UL64(0xD186B8C721C0C207),
UL64(0xEADA7DD6CDE0EB1E), UL64(0xF57D4F7FEE6ED178),
UL64(0x06F067AA72176FBA), UL64(0x0A637DC5A2C898A6),
UL64(0x113F9804BEF90DAE), UL64(0x1B710B35131C471B),
UL64(0x28DB77F523047D84), UL64(0x32CAAB7B40C72493),
UL64(0x3C9EBE0A15C9BEBC), UL64(0x431D67C49C100D4C),
UL64(0x4CC5D4BECB3E42B6), UL64(0x597F299CFC657E2A),
UL64(0x5FCB6FAB3AD6FAEC), UL64(0x6C44198C4A475817)
};
void crypto_sha384_sha512_init(sha512_ctx_t *ctx, int32_t is_384)
{
SHA512_VALIDATE( ctx != NULL );
memset( ctx, 0, sizeof( sha512_ctx_t ) );
ctx->total[0] = 0;
ctx->total[1] = 0;
if( is_384 == 0 ) {
/* SHA-512 */
ctx->state[0] = UL64(0x6A09E667F3BCC908);
ctx->state[1] = UL64(0xBB67AE8584CAA73B);
ctx->state[2] = UL64(0x3C6EF372FE94F82B);
ctx->state[3] = UL64(0xA54FF53A5F1D36F1);
ctx->state[4] = UL64(0x510E527FADE682D1);
ctx->state[5] = UL64(0x9B05688C2B3E6C1F);
ctx->state[6] = UL64(0x1F83D9ABFB41BD6B);
ctx->state[7] = UL64(0x5BE0CD19137E2179);
} else {
/* SHA-384 */
ctx->state[0] = UL64(0xCBBB9D5DC1059ED8);
ctx->state[1] = UL64(0x629A292A367CD507);
ctx->state[2] = UL64(0x9159015A3070DD17);
ctx->state[3] = UL64(0x152FECD8F70E5939);
ctx->state[4] = UL64(0x67332667FFC00B31);
ctx->state[5] = UL64(0x8EB44A8768581511);
ctx->state[6] = UL64(0xDB0C2E0D64F98FA7);
ctx->state[7] = UL64(0x47B5481DBEFA4FA4);
}
ctx->is_384 = is_384;
}
void crypto_sha512_init( sha512_ctx_t *ctx )
{
crypto_sha384_sha512_init(ctx, 0);
}
static int32_t local_sha512_process( sha512_ctx_t *ctx,
const uint8_t data[128] )
{
int32_t i;
uint64_t temp1, temp2, W[80];
uint64_t A, B, C, D, E, F, G, H;
SHA512_VALIDATE_RET( ctx != NULL );
SHA512_VALIDATE_RET( (const uint8_t *)data != NULL );
#define SHR(x,n) (x >> n)
#define ROTR(x,n) (SHR(x,n) | (x << (64 - n)))
#define S0(x) (ROTR(x, 1) ^ ROTR(x, 8) ^ SHR(x, 7))
#define S1(x) (ROTR(x,19) ^ ROTR(x,61) ^ SHR(x, 6))
#define S2(x) (ROTR(x,28) ^ ROTR(x,34) ^ ROTR(x,39))
#define S3(x) (ROTR(x,14) ^ ROTR(x,18) ^ ROTR(x,41))
#define F0(x,y,z) ((x & y) | (z & (x | y)))
#define F1(x,y,z) (z ^ (x & (y ^ z)))
#define P(a,b,c,d,e,f,g,h,x,K) \
{ \
temp1 = h + S3(e) + F1(e,f,g) + K + x; \
temp2 = S2(a) + F0(a,b,c); \
d += temp1; h = temp1 + temp2; \
}
for( i = 0; i < 16; i++ ) {
GET_UINT64_BE( W[i], data, i << 3 );
}
for( ; i < 80; i++ ) {
W[i] = S1(W[i - 2]) + W[i - 7] +
S0(W[i - 15]) + W[i - 16];
}
A = ctx->state[0];
B = ctx->state[1];
C = ctx->state[2];
D = ctx->state[3];
E = ctx->state[4];
F = ctx->state[5];
G = ctx->state[6];
H = ctx->state[7];
i = 0;
do {
P( A, B, C, D, E, F, G, H, W[i], K[i] ); i++;
P( H, A, B, C, D, E, F, G, W[i], K[i] ); i++;
P( G, H, A, B, C, D, E, F, W[i], K[i] ); i++;
P( F, G, H, A, B, C, D, E, W[i], K[i] ); i++;
P( E, F, G, H, A, B, C, D, W[i], K[i] ); i++;
P( D, E, F, G, H, A, B, C, W[i], K[i] ); i++;
P( C, D, E, F, G, H, A, B, W[i], K[i] ); i++;
P( B, C, D, E, F, G, H, A, W[i], K[i] ); i++;
} while( i < 80 );
ctx->state[0] += A;
ctx->state[1] += B;
ctx->state[2] += C;
ctx->state[3] += D;
ctx->state[4] += E;
ctx->state[5] += F;
ctx->state[6] += G;
ctx->state[7] += H;
return( 0 );
}
/*
* SHA-512 process buffer
*/
void crypto_sha512_update( sha512_ctx_t *ctx,
const uint8_t *data,
uint32_t len )
{
int32_t ret;
uint32_t fill;
uint32_t left;
SHA512_VALIDATE( ctx != NULL );
SHA512_VALIDATE( len == 0 || data != NULL );
left = (uint32_t) (ctx->total[0] & 0x7F);
fill = 128 - left;
ctx->total[0] += (uint64_t) len;
if( ctx->total[0] < (uint64_t) len ) {
ctx->total[1]++;
}
if( left && len >= fill ) {
memcpy( (void *) (ctx->buffer + left), data, fill );
if( ( ret = local_sha512_process( ctx, ctx->buffer ) ) != 0 ) {
/* error */
return ;
}
data += fill;
len -= fill;
left = 0;
}
while( len >= 128 ) {
if( ( ret = local_sha512_process( ctx, data ) ) != 0 ) {
/* error */
return ;
}
data += 128;
len -= 128;
}
if( len > 0 ) {
memcpy( (void *) (ctx->buffer + left), data, len );
}
}
/*
* SHA-512 final digest
*/
void crypto_sha512_final( sha512_ctx_t *ctx, uint8_t *digest )
{
int32_t ret;
unsigned used;
uint64_t high, low;
SHA512_VALIDATE( ctx != NULL );
SHA512_VALIDATE( (uint8_t *)digest != NULL );
/*
* Add padding: 0x80 then 0x00 until 16 bytes remain for the length
*/
used = ctx->total[0] & 0x7F;
ctx->buffer[used++] = 0x80;
if( used <= 112 ) {
/* Enough room for padding + length in current block */
memset( ctx->buffer + used, 0, 112 - used );
} else {
/* We'll need an extra block */
memset( ctx->buffer + used, 0, 128 - used );
if( ( ret = local_sha512_process( ctx, ctx->buffer ) ) != 0 ) {
/* error */
return ;
}
memset( ctx->buffer, 0, 112 );
}
/*
* Add message length
*/
high = ( ctx->total[0] >> 61 )
| ( ctx->total[1] << 3 );
low = ( ctx->total[0] << 3 );
PUT_UINT64_BE( high, ctx->buffer, 112 );
PUT_UINT64_BE( low, ctx->buffer, 120 );
if( ( ret = local_sha512_process( ctx, ctx->buffer ) ) != 0 ) {
/* error */
return ;
}
/*
* Output final state
*/
PUT_UINT64_BE( ctx->state[0], digest, 0 );
PUT_UINT64_BE( ctx->state[1], digest, 8 );
PUT_UINT64_BE( ctx->state[2], digest, 16 );
PUT_UINT64_BE( ctx->state[3], digest, 24 );
PUT_UINT64_BE( ctx->state[4], digest, 32 );
PUT_UINT64_BE( ctx->state[5], digest, 40 );
if( ctx->is_384 == 0 ) {
PUT_UINT64_BE( ctx->state[6], digest, 48 );
PUT_UINT64_BE( ctx->state[7], digest, 56 );
}
}
测试用例
针对SHA512导出的三个接口,我编写了以下测试用例:
#include
#include
#include "sha512.h"
#include "convert.h"
int log_hexdump(const char *title, const unsigned char *data, int len)
{
char str[160], octet[10];
int ofs, i, k, d;
const unsigned char *buf = (const unsigned char *)data;
const char dimm[] = "+------------------------------------------------------------------------------+";
printf("%s (%d bytes):\r\n", title, len);
printf("%s\r\n", dimm);
printf("| Offset : 00 01 02 03 04 05 06 07 08 09 0A 0B 0C 0D 0E 0F 0123456789ABCDEF |\r\n");
printf("%s\r\n", dimm);
for (ofs = 0; ofs < (int)len; ofs += 16) {
d = snprintf( str, sizeof(str), "| %08X: ", ofs );
for (i = 0; i < 16; i++) {
if ((i + ofs) < (int)len) {
snprintf( octet, sizeof(octet), "%02X ", buf[ofs + i] );
} else {
snprintf( octet, sizeof(octet), " " );
}
d += snprintf( &str[d], sizeof(str) - d, "%s", octet );
}
d += snprintf( &str[d], sizeof(str) - d, " " );
k = d;
for (i = 0; i < 16; i++) {
if ((i + ofs) < (int)len) {
str[k++] = (0x20 <= (buf[ofs + i]) && (buf[ofs + i]) <= 0x7E) ? buf[ofs + i] : '.';
} else {
str[k++] = ' ';
}
}
str[k] = '\0';
printf("%s |\r\n", str);
}
printf("%s\r\n", dimm);
return 0;
}
int main(int argc, const char *argv[])
{
const char *data = "C1D0F8FB4958670DBA40AB1F3752EF0D";
const char *digest_exp_str = "D2A72FDEFB6C5B3C8DB639869C6BC756EBD11B1D152B29CF55011C31DE0F3807D21C357C583619EE9006B7E4023042200394DC1DDE913463EC6000AA472D8D24";
uint8_t digest_calc[SHA512_DIGEST_LEN];
uint8_t digest_exp_hex[SHA512_DIGEST_LEN];
sha512_ctx_t ctx;
const char *p_calc = data;
uint8_t data_bytes[128];
uint16_t len_bytes;
char data_str[128];
if (argc > 1) {
p_calc = argv[1];
}
utils_hex_string_2_bytes(data, data_bytes, &len_bytes);
log_hexdump("data_bytes", data_bytes, len_bytes);
utils_bytes_2_hex_string(data_bytes, len_bytes, data_str);
printf("data_str: %s\n", data_str);
if (!strcmp(data, data_str)) {
printf("hex string - bytes convert OK\n");
} else {
printf("hex string - bytes convert FAIL\n");
}
crypto_sha512_init(&ctx);
crypto_sha512_update(&ctx, (uint8_t *)p_calc, strlen(p_calc));
crypto_sha512_final(&ctx, digest_calc);
utils_hex_string_2_bytes(digest_exp_str, digest_exp_hex, &len_bytes);
if (len_bytes == sizeof(digest_calc) && !memcmp(digest_calc, digest_exp_hex, sizeof(digest_calc))) {
printf("SHA512 digest test OK\n");
log_hexdump("digest_calc", digest_calc, sizeof(digest_calc));
} else {
log_hexdump("digest_calc", digest_calc, sizeof(digest_calc));
log_hexdump("digest_exp", digest_exp_hex, sizeof(digest_exp_hex));
printf("SHA512 digest test FAIL\n");
}
return 0;
}
测试用例比较简单,就是对字符串C1D0F8FB4958670DBA40AB1F3752EF0D进行SHA1运算,期望的摘要结果的hexstring是D2A72FDEFB6C5B3C8DB639869C6BC756EBD11B1D152B29CF55011C31DE0F3807D21C357C583619EE9006B7E4023042200394DC1DDE913463EC6000AA472D8D24,这个期望值是用算法工具算出来的。
先用API接口算出摘要值,再与期望值比较,这里有个hexstringtobyte的转换,如果比较一致则表示API计算OK;反之,接口计算失败。
同时,也欢迎大家设计提供更多的测试案例代码。
github仓库
以上代码和测试用例,及编译运行等,可以参考我的github仓库,有详细的流程介绍,欢迎大家交流讨论。如果有帮助到你的话,记得帮忙点亮一颗星哦。
更多参考链接
[1] 【安全算法的github仓库】
[2] 【安全算法之概述】一文带你简要了解常见常用的安全算法
-
C语言
+关注
关注
180文章
7604浏览量
136678 -
源码
+关注
关注
8文章
639浏览量
29184 -
安全算法
+关注
关注
0文章
9浏览量
6102
发布评论请先 登录
相关推荐
基于FPGA芯片HMAC_SHA1_96计算术运算单元的硬件设计
信息摘要算法之二:SHA1算法分析及实现
hashcalc校验器下载
基于SHA-1算法的硬件设计及实现(FPGA实现)
哈希算法SHA-512的基本概念及特性解析
比特币为什么需要采用SHA-256算法
基于STM32的C语言SHA256加密算法



 【安全算法之SHA512】SHA512摘要运算C语言源码实现
【安全算法之SHA512】SHA512摘要运算C语言源码实现









评论